Blog Runas Savecred
Run as administrator from standard user with runas savecred command
Run application with administrator privileges as normal user without administrator rights by runas command in Windows.
Use runas in command line, in a batch file or a shortcut with the program.exe you want to run as administrator.
In example my program.exe is >> cmd.exe << and my administrator account is my local administrator account >> localadmin <<.
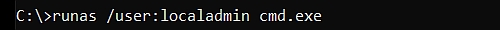
My command is
>> runas /user:localadmin cmd.exe <<
After execute this runas command, you will be asked to enter the password of the administrator account.
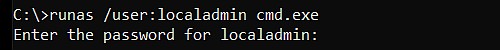
You cannot pass the password to runas command as argument,
but with the parameter savecred you can store credentials in credential manager, to avoid entering the password on each call.
>> runas /user:localadmin /savecred cmd.exe <<
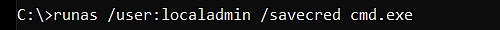
Now you are asked for the password only once, the next calls with savecred parameter you don't have to enter this password to run this application as administrator.
Beside the missing password parameter, there are two other problems with runas savecred
1. It is not recommended, because username and password are stored in the windows credential manager of this profile and
can used to execute every program with credentials of the administrator.
Better storing the credentials for each program separate, instead of using runas savecred.
2. The application is not running with elevated privileges or it is blocked by the UAC (User Access Control).
As solution you can allow specific applications to run with administrator permissions, elevated privileges and bypass the UAC
This can do by
1. using an encrypted file with administrator credentials only for the authorized application
or
2. an application manager that control selected application to run as administrator.
Both is not possible with runas savecred, but the following simple solutions can do it.
1. RunAsSpc store login information for each application in a separate encrypted file.
or
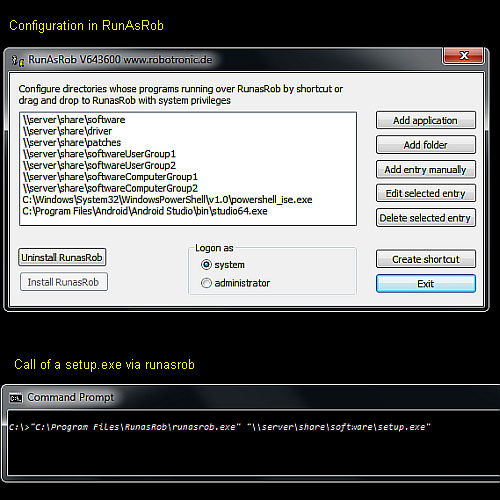
2. RunAsRob manage and start applications with administrator rights and elevated privileges from a user account.
With RunAsRob you can authorize specific applications or complete folders and its contents you want to allow running with administrator privileges.
By this tool you can limit administrator rights to a few applications or delegate particular administrator tasks fast and easy.
The principle is very simple, clear to understand, safe and easy to configure.
You just have to authorize the task, folder or program file.
After the application.exe run via runasrob.exe, RunAsRob compare this application and its path if it is an allowed directory and start the application with appropriate rights.
A call can do by drag and drop application.exe over runasrob.exe, a shortcut, a script or any other way by the command
>> C:\Program Files\RunasRob\runasrob.exe C:\path\application.exe <<
RunAsRob Screenshot
There are lot of other runas tools or utilities you can run application with administrator rights.
- You find a site which compare that tools and list the various options on
Run application as administrator, Runas alternative - Runas in Wikipedia
- Runas tutorial of Microsoft
Date: 2024-06-02
Data protection
Imprint